
Whitespots Portal and ISO 27001 Certification
1. 📋 What is ISO 27001 — and Why Does It Matter?
ISO/IEC 27001 is the world’s best-known standard for information security management systems (ISMS). It defines the requirements an ISMS must meet and provides companies of any size and from all sectors with guidance for establishing, implementing, maintaining, and continually improving their approach to information security.
For technology companies in particular, ISO 27001 has become a baseline expectation - one that opens doors with enterprise clients, satisfies investor due diligence, and increasingly determines whether cyber insurance is even available.
2. 🏢 About the Clients
- Company: Multiple Companies
- Industry: Software Development, Hosting, Payment Institutions, Outsource Development
- Region: Global
This case is applicable to virtually any niche and represents a typical scenario for companies facing the need to obtain ISO 27001 certification. When companies decide to pursue ISO 27001 certification, they often don’t know where to start - the requirements are extensive, and mapping them to concrete technical solutions is rarely obvious without prior experience.
Whitespots has proven experience helping diverse companies achieve certification and can provide valuable insights throughout the process. Among our clients pursuing ISO 27001:
- Hosting providers
- Payment institutions
- Outsource development companies
All these companies share a common need: demonstrating mature application security processes to obtain certification, pass audits, and meet requirements from investors and insurance companies. Whether you’re a fast-growing startup facing your first investor audit, an established company purchasing cyber insurance, or a service provider requiring certification for client contracts, establishing proper vulnerability management is critical.
Vulnerability management is consistently one of the most challenging yet essential areas for ISO 27001 certification. It demonstrates organizational maturity in handling security risks, closes multiple ISO controls related to technical vulnerability management, change management, and security monitoring, and provides auditors with tangible evidence of a systematic approach to application security.
Without a functioning vulnerability management process, auditors view your security posture as chaotic and immature - regardless of what other security measures you have in place. Whitespots Portal addresses this critical gap and enables companies to quickly establish the mature, functioning process that certification requires.
“ISO 27001 certification requires companies to establish a clear security framework and demonstrate genuine understanding of how it works in practice. The Portal helps teams build exactly that kind of mature vulnerability management approach, which is why so many of our clients successfully use it to achieve certification.”
 Maxim Mosharov
Whitespots CEO
Maxim Mosharov
Whitespots CEO
3. 🎯Background and Project Goals: The ISO 27001 Challenge
Before implementing Whitespots Portal, companies faced a critical problem: the lack of a structured approach to application security made it impossible to pass IT audits and obtain ISO 27001 certification.
The Portal became the ideal solution for addressing vulnerability management control as part of the certification project.
Main Problems
1. Chaotic Security Process Organization
All processes were scattered with nothing unified. The lack of a centralized approach to vulnerability management created the impression of a complete absence of process in the eyes of auditors.
2. Pressure from Investors and Insurance Companies
Often companies had investors who periodically came with their own audits and asked many questions about application security. The company had nothing to show regarding automated checks.
When purchasing cyber risk insurance, insurance companies also conduct their own IT audits. The abundance of these IT audits created additional burden: each one required demonstrating and proving the existence of processes.
3. Lack of Automated AppSec Processes
Companies only had scattered scanners that someone occasionally ran. Some teams conducted code reviews, looked at things independently, and ran some checks once a year.
4. Lack of Continuous Vulnerability Detection Security scanning conducted on an irregular or infrequent basis provides limited visibility into the actual state of an organization’s codebase. Each commit introduces potential vulnerabilities that remain undetected until the next scan cycle. For organizations that deploy code regularly, the gap between scans represents a significant and unmanaged risk window.
Auditor’s Opinion:
“When I see scattered scanners running occasionally with no centralized tracking or remediation workflow, that’s not a security process - that’s just ad-hoc activity. Companies might be ‘doing something,’ but without a systematic approach to vulnerability management, there’s no evidence of control or maturity. This consistently becomes a major finding during certification audits.”
 ISO 27001 Auditor
ISO 27001 Auditor
4. Inability to Quickly Demonstrate Results
The main problem was the need to quickly show results with a complete absence of application security processes.
Attempts to show that there was code review or periodic checks didn’t look serious to auditors. This was perceived not as a process, but as chaotic actions without understanding of effectiveness.
5. Multiple Audits Require a Unified Approach
Given that companies undergo checks from:
- Investors
- Insurance companies
- ISO 27001 auditors
The need to repeatedly prove and demonstrate security processes each time created critical overhead.
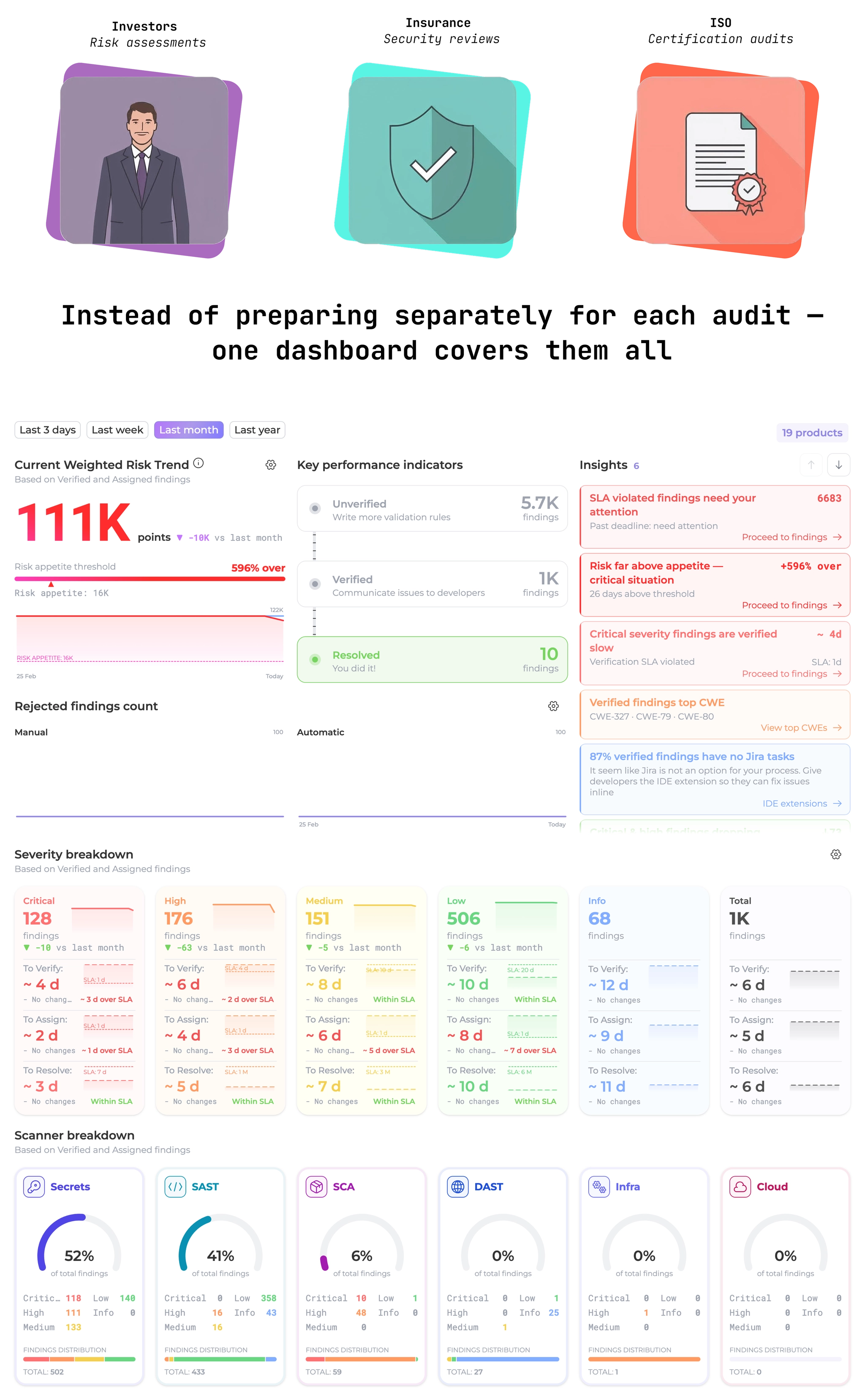
“Our clients face audits from multiple sources - investors, insurers, ISO auditors. Instead of scrambling to prepare different reports each time, they simply pull up the Portal dashboard, export what’s needed, and send it over. One source of truth for all stakeholders.”
 Maxim Mosharov
Whitespots CEO
Maxim Mosharov
Whitespots CEO
4. ✨ Why Whitespots Portal for ISO 27001
Solving the Key ISO 27001 Task
Whitespots Portal helps close not all ISO 27001 controls, but sufficiently heavy parts related to vulnerability management and application security.
Controls fully covered by Whitespots Portal:
5.9 Inventory of information and other associated assets. Automatic discovery of subdomains and repositories, mapped to products with business criticality assigned.
8.8 Management of technical vulnerabilities. The core of what the Portal does: systematic identification, evaluation, and remediation tracking of vulnerabilities across all assets.
8.9 Configuration management. Scanner findings surface misconfigurations - evidence that configuration is being monitored.
8.25 Secure development lifecycle. The Portal provides the scanning and tracking layer.
8.29 Security testing in development and acceptance. Automated scanning integrated into the development lifecycle provides documented evidence of security testing before release.
8.32 Change management. The Portal tracks remediation activity and links findings to changes.
Controls partially addressed by Whitespots Portal:
8.15 Logging and 8.16 Monitoring activities. The Portal aggregates findings, tracks changes over time, and provides auditors with a documented history of security issues and remediation dynamics.
8.26 Application security requirements and 8.28 Secure coding. Portal findings inform and document where these requirements are being met or violated.
8.27 Secure system architecture and engineering principles. Architecture review evidence can be supported by Portal findings, but formal documentation of principles sits outside the tool.
Whitespots Solution Advantages
- Quick Implementation: ability to start work within the pilot period
- Unified Approach: single platform for all AppSec processes
- Easy Demonstration: easy to generate reports and screenshots for auditors
- Build from Scratch: complete process implementation from scratch for companies without existing AppSec infrastructure
- Automatic Asset Discovery subdomains and repositories found automatically, mapped to products with business criticality assigned — no spreadsheets required.
“We knew we needed ISO 27001, but had no idea where to even start with vulnerability management. Do we hire consultants? Build everything ourselves? Whitespots provided not just the platform, but useful guidance on the entire process - we could see our security posture immediately and start showing progress within the first week.”
 Client’s CISO
Client’s CISO
5. 📌Key Tasks for ISO 27001 Implementation
To solve the problems and achieve ISO 27001 certification, the following tasks were defined:
1. Portal Installation and Deployment
Set up the portal in the client’s infrastructure and conduct all installation work. This includes configuring integrations with existing development tools, setting up user roles and permissions, and establishing scanning policies aligned with the company’s risk tolerance and compliance requirements.
2. Quick Scanning and Vulnerability Detection
Conduct initial comprehensive scanning of client assets to establish a security baseline. This first scan reveals technical deficiencies across the infrastructure and provides immediate visibility into the current security posture - something many companies lack entirely before starting their ISO journey.
3. Creating Progress Visualization
Ensure the formation of clear graphs and metrics in Whitespots Portal that demonstrate risk reduction over time. Teams can log in to the Whitespots Portal dashboard at any time to track real-time progress.
Within a week, clients should see measurable changes in their security metrics, and progress in vulnerability remediation should become visible and trackable. This visualization is crucial for auditors, who need to see not just current state, but evidence of continuous improvement and systematic remediation processes.
4. Generating Audit Reports
Generate comprehensive reports on key vulnerabilities that were identified, prioritized, and remediated by the company. These reports provide auditors with tangible evidence of a functioning Vulnerability Management process - showing not just that vulnerabilities are found, but that they’re being systematically addressed according to risk-based prioritization.
5. Addressing Remaining ISO 27001 Requirements
Final Goal: Companies that implemented the portal should obtain ISO 27001 certificates.
With vulnerability management established through Whitespots Portal, companies now have a solid technical foundation - but ISO 27001 certification requires more. Beyond the technical controls that the Portal addresses, organizations must develop comprehensive policies, procedures, organizational controls, physical security measures, and documentation across all domains of the standard.
The Portal specifically covers critical technical controls related to vulnerability management, application security, and security monitoring. These are often the most challenging technical components for companies without established AppSec infrastructure. However, achieving certification also requires addressing areas like information security policies, access control procedures, incident response plans, business continuity planning, supplier management, and employee training programs.
Companies should view the Portal as the foundation for their technical security controls while working with consultants or internal teams to address the full scope of ISO 27001 requirements.
Whitespots provides guidance and support throughout this process, helping clients understand which policies and procedures they need and how to implement them effectively.
“We don’t just provide the Portal and walk away. Our team has extensive experience with various security certifications and we actively guide clients through the entire process, from technical implementation to understanding which policies and procedures they need. We want our clients to succeed in getting certified, not just in using our software.”
 Maxim Mosharov
Whitespots CEO
Maxim Mosharov
Whitespots CEO
6. 🛠️ Implementation Stages
1. Pilot, Installation, and Initial Assessment (First 2 Weeks)
Clients receive up to two weeks of free piloting from Whitespots. During this initial phase, the portal is deployed in the client’s infrastructure with all necessary integrations configured. Even within the pilot period, companies can immediately conduct comprehensive scanning of their assets, obtain first security metrics, and begin demonstrating tangible progress toward ISO 27001 goals.
This rapid deployment means that within days, organizations go from having no visibility into their vulnerability landscape to having a complete, functioning assessment of their security posture - providing the foundation for all subsequent certification work.
2. Vulnerability Remediation and Metrics Formation
The client remediates identified technical deficiencies. Within a week, changes appear in the graphs, and progress in vulnerability remediation becomes visible.
This is critical for auditing - you can record and show auditors the dynamics of security improvement.
5. Preparation for ISO 27001 Audit
Forming necessary documentation and reports for auditors.
“The pilot period exceeded our expectations. Within days, we had complete visibility into our security posture - something we’d been struggling to achieve for months. Two weeks in, we were already presenting concrete metrics to our board and showing consistent week-over-week improvement.”
 Client’s CISO
Client’s CISO
7.✅ Whitespots Portal Implementation Results
 Creation of Vulnerability Management Process
Creation of Vulnerability Management Process
Companies now have a full-fledged vulnerability management process that was previously completely absent.
Closing Relevant ISO 27001 Controls
Whitespots Portal helped close ISO 27001 controls related to technical vulnerability management.
Simplifying Communication with Auditors
Instead of having to repeatedly prove the existence of security processes to different auditors, companies can now quickly log in to Whitespots Portal to generate audit-ready reports, track remediation progress, and export compliance documentation.
Teams can provide screenshots with metrics and demonstrate the dynamics of vulnerability remediation - eliminating the need for manual data compilation across multiple tools.
Progress Visibility
Graphs in the portal show how risk is going down, which is critical proof for auditors of the effectiveness of AppSec processes.
| Metric | Before Whitespots | After Whitespots |
|---|---|---|
| Vulnerability Management Process | Absent | Fully Implemented |
| ISO 27001 Controls (AppSec) | Not Closed | Closed |
| Time to Prepare Audit Reports | Not existed | Portal Screenshots in Minutes |
| AppSec Automation | Scattered Scanners | Unified Process |
8. 🗣️ Client Feedback
“Before Whitespots, our ISO 27001 audit prep felt overwhelming. We had tools running, but no cohesive process - auditors saw right through it. The Portal gave us exactly what we needed: a mature, documented vulnerability management framework that stood up to scrutiny. We achieved certification on our first audit attempt, and our insurance premiums actually decreased once we could demonstrate proper security controls. It’s rare to find a solution that delivers both compliance value and genuine operational improvement.”
 Client’s CISO
Client’s CISO
9. ➡️ Next Steps: Deepening Security with Whitespots Portal
After establishing the foundational vulnerability management process for certification, many clients expand their use of the Portal to enhance overall application security maturity.
This includes integrating additional security scanners, implementing custom validation rules specific to their technology stack, establishing more granular SLA tracking for different vulnerability categories, and extending coverage to include cloud infrastructure and containerized environments.
The Portal’s flexibility allows companies to grow their AppSec capabilities progressively without disrupting the processes that already passed audit.


